In today’s hyper-connected world, where digital transformation is no longer an aspiration but a fundamental business imperative, organizations face an increasingly complex and dynamic threat landscape. The promise of advanced technologies like AI, cloud computing, and IoT comes hand-in-hand with unprecedented vulnerabilities. For business leaders, IT professionals, and technology enthusiasts alike, understanding and effectively managing information technology risk and controls is paramount. It’s about more than just preventing breaches; it’s about safeguarding reputation, ensuring operational continuity, and securing the foundation for future innovation. Today, Daily98news will accompany you to explore the critical dimensions of IT risk and the robust control strategies necessary to thrive in this challenging environment.
Understanding the Evolving Landscape of It Risks
The digital realm is a double-edged sword, offering immense opportunities while simultaneously presenting an array of complex risks. Modern enterprises operate within an intricate web of interconnected systems, making them susceptible to a broad spectrum of threats that constantly evolve in sophistication and scale. Staying ahead requires continuous vigilance and a deep understanding of these shifting risk paradigms.
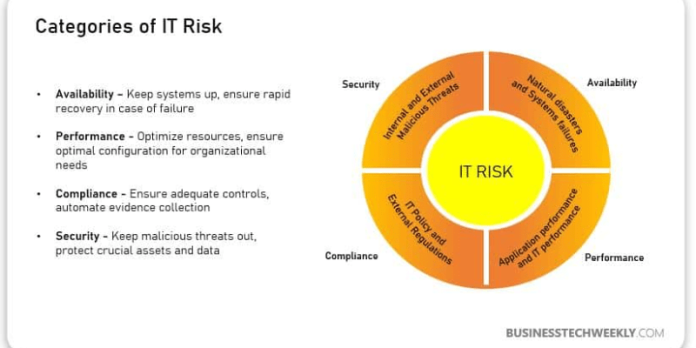
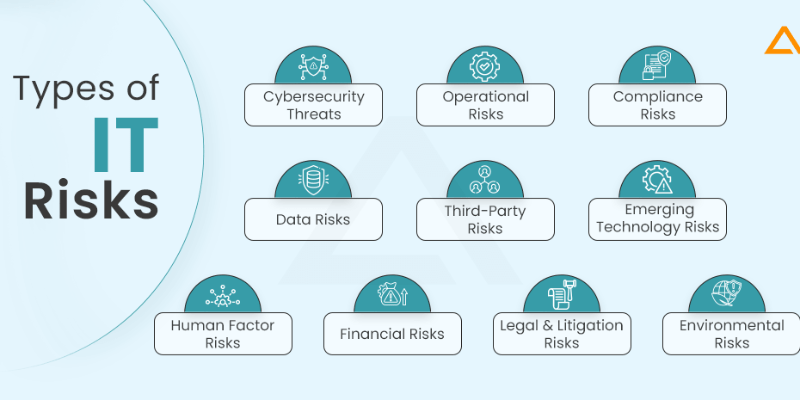
Types of contemporary It risks
The spectrum of IT risks is vast, encompassing everything from malicious cyberattacks to unforeseen operational failures and non-compliance with regulatory mandates. Cyber risks remain at the forefront, with threats such as ransomware, phishing, and advanced persistent threats (APTs) becoming increasingly sophisticated. Operational risks, including human error, system outages, and software vulnerabilities, can disrupt critical business functions. Furthermore, compliance risks stemming from stringent data privacy regulations like GDPR or industry-specific mandates can result in significant financial penalties and reputational damage if not properly addressed. A new vulnerability is identified every 17 minutes, highlighting the continuous emergence of potential threats.
Impact of emerging technologies on risk profiles
Emerging technologies, while transformative, also introduce novel attack vectors and amplify existing risks. Cloud computing, for instance, offers scalability but shifts some responsibility for security to the cloud provider while expanding the attack surface for organizations using multiple public cloud providers. The proliferation of IoT devices creates countless new endpoints that can be exploited, often lacking robust native security features. Artificial intelligence, a powerful tool for defense, can also be weaponized by adversaries, leading to more sophisticated AI-driven malware and attacks. The adoption of AI is rapidly outpacing the establishment of governance frameworks, with a significant majority of organizations currently lacking fully embedded controls to manage associated risks.
The cost of It breaches and control failures
The financial fallout. The global average cost of a data breach reached $4.88 million in 2024, representing a 10% increase, averaging $10.10 million in 2024, followed by the financial sector at $6.08 million. Beyond direct costs, organizations face expenses for legal counsel, customer notifications, credit monitoring, and regulatory fines. The overall economic impact of cybercrime is projected to be $10.5 trillion globally in 2025, underscoring the immense financial stakes involved in robust information technology risk and controls.
The Core Principles of Information Technology Risk Management
Effective management of IT risks is not merely a technical exercise; it is a strategic business imperative that requires a structured, continuous approach. Companies must integrate risk considerations into every layer of their operations,.
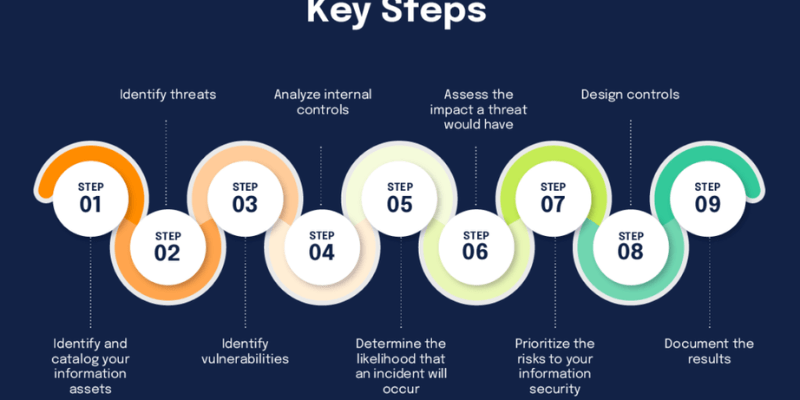
Risk identification and assessment methodologies
The first step in any robust risk management program is to systematically identify and assess potential threats and vulnerabilities. This involves evaluating all IT assets—hardware, software, data, and networks—to understand their criticality and potential exposure. Methodologies often include threat modeling, vulnerability scanning, and penetration testing, which simulate attacks to uncover weaknesses. Risk assessments quantify the likelihood and potential impact of identified risks, allowing organizations to prioritize their efforts effectively. This crucial phase provides the foundational intelligence needed to develop targeted control strategies.
Risk mitigation strategies
Once risks are identified and assessed, organizations must choose appropriate mitigation strategies. These typically fall into four categories: risk avoidance, where activities posing unacceptable risks are halted; risk transfer, such as through cybersecurity insurance; risk acceptance, for low-impact risks that are monitored; and risk reduction, which involves implementing controls to lower the likelihood or impact of a risk event. The objective is to strike a balance between security and business enablement, ensuring that protective measures do not unduly hinder innovation or operational efficiency.
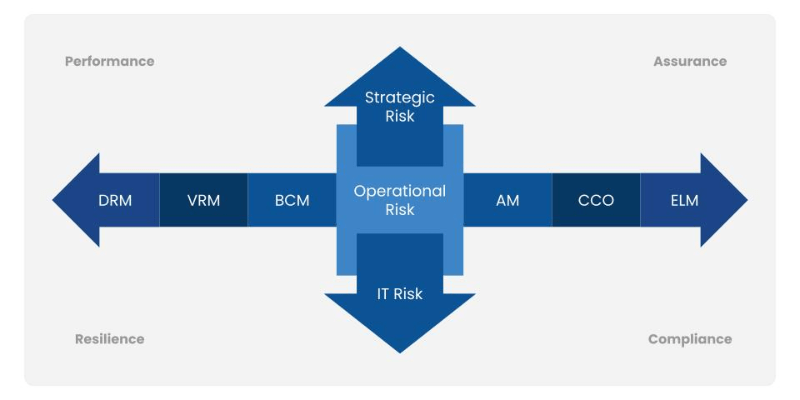
The role of governance in It risk
Effective IT risk management is deeply rooted in strong governance. This involves establishing clear policies, roles, and responsibilities for managing IT risks across the organization. Senior leadership and boards of directors must actively champion a culture of vigilance, training, and accountability. As Allison Dunn, a security expert, states, “Cybersecurity isn’t an IT issue—it’s a leadership issue. The smartest leaders don’t just fund security; they champion a culture where vigilance, training, and accountability are non-negotiable.” Governance frameworks ensure that risk management processes are consistent, transparent, and aligned with overall business objectives, integrating cybersecurity as a strategic business enabler rather than merely a cost center.
Key Information Technology Controls for Modern Enterprises
Controls are the practical mechanisms by which organizations manage and reduce their IT risks. They act as safeguards, designed to prevent, detect, and respond to threats effectively. A layered defense approach, incorporating various types of controls, is essential to build resilience against the diverse and evolving threat landscape. James Scott notes that “There’s no silver bullet solution with cyber security; a layered defense is the only viable defense.”
Technical controls
Technical controls are technology-based mechanisms embedded within IT systems to protect assets. These include sophisticated access management systems, which ensure only authorized users can access sensitive data and systems, often leveraging multi-factor authentication. Encryption technologies secure data at rest and in transit, rendering it unreadable to unauthorized parties. Firewalls and intrusion detection/prevention systems monitor network traffic, blocking malicious activity and alerting security teams to suspicious patterns. Regular patching and vulnerability management are also critical technical controls, as a significant percentage of data breaches are caused by a failure to patch known vulnerabilities.
Administrative controls
Administrative controls are policies, procedures, and guidelines established by management to govern the behavior of individuals and the management of IT systems. Examples include comprehensive security policies outlining acceptable use, data handling, and incident response protocols. Regular security awareness training for employees is vital, as the human element remains a common root cause of data breaches, often due to negligence or social engineering. Clear operational procedures for system configuration, change management, and backup and recovery ensure consistency and reduce the risk of errors. These controls cultivate a culture of security throughout the organization, extending beyond technical safeguards.
Physical controls
Physical controls protect IT assets, comprehensive physical security forms a fundamental layer of information technology risk and controls.
Implementing Robust Control Frameworks
Adopting industry-recognized control frameworks provides a structured approach to implementing, managing, and continuously improving IT security. These frameworks offer best practices, standards, and guidelines that help organizations assess their current security posture, identify gaps, and build a more resilient defense. The benefits extend beyond compliance, fostering a proactive security culture.
Popular frameworks and standards
Several widely adopted frameworks guide organizations in managing their cybersecurity risks. The National Institute of Standards and Technology (NIST) Cybersecurity Framework (CSF) 2.0 provides guidance to manage cybersecurity risks, usable by any organization regardless of size or sector. It is a popular choice, particularly within the technology industry, with 40% of US organizations using it. ISO 27001 is another globally recognized standard for information security management systems, offering a systematic approach to managing sensitive company information. COBIT (Control Objectives for Information and Related Technologies) provides a comprehensive framework for IT governance and management, helping to ensure IT aligns with business objectives. Many organizations, in fact, leverage multiple frameworks to guide their security efforts, indicating a layered approach to cybersecurity.
Steps for effective implementation and continuous monitoring
Implementing a control framework is a multi-step process that begins with assessing the organization’s current state against the framework’s guidelines. This gap analysis informs the development of a roadmap for implementing necessary controls and processes. Continuous monitoring is crucial, involving regular audits, performance metrics, and risk assessments to ensure controls remain effective and adapt to new threats. Organizations that identify and address breaches within 200 days generally incur 23% less cost than those with longer containment times. Leveraging integrated risk management (IRM) solutions can offer a holistic view of risk management, combining technology, process, and data for simplification, automation, and integration of strategic and operational management processes.
Integrating controls with business processes
The most effective controls are those seamlessly integrated into daily business operations, becoming an intrinsic part of how work is done rather than an isolated security layer. This requires collaboration between IT, security, and business units to ensure controls support business objectives without creating unnecessary friction. For example, secure-by-design principles ensure security is built into new applications and systems.
Leveraging AI and Automation in Risk and Control
Artificial intelligence and automation are rapidly transforming the landscape of information technology risk and controls, offering powerful new capabilities for threat detection, response, and compliance. While these technologies present their own set of risks, their strategic application can significantly enhance an organization’s security posture.
Ai for threat detection and anomaly identification
AI-powered systems excel at processing vast quantities of data in real-time, identifying subtle patterns and anomalies that human analysts might miss. Machine learning algorithms continuously learn, AI-driven malware that can mutate to avoid static detection. AI enhances threat intelligence, automates response mechanisms, and proactively identifies vulnerabilities, drastically improving the speed and accuracy of threat detection and analysis.
Automation in compliance and audit processes
Automation streamlines routine security tasks, such as updating security protocols, patching vulnerabilities, and managing access controls. This reduces the burden on cybersecurity teams, freeing them to focus on more complex and strategic initiatives. In compliance, automation can facilitate continuous monitoring of IT estates, generate audit trails, and prepopulate risk data, making it easier to demonstrate adherence to regulatory requirements and internal policies. This not only improves efficiency but also enhances the accuracy and timeliness of compliance reporting, transforming traditionally labor-intensive processes.
Predictive analytics for emerging risks
Beyond reactive detection, AI enables predictive analysis by examining historical data and current trends to anticipate potential attack vectors before a breach occurs. This proactive application of AI significantly strengthens an organization’s overall security posture. Predictive models can identify vulnerabilities and emerging threats, allowing security teams to implement preventative measures and allocate resources more effectively. The ability to forecast risks empowers organizations to build resilience and adapt their information technology risk and controls to stay ahead of the curve, moving.
Case Studies: Real-World Application of It Controls
Examining practical applications of IT controls across various industries provides valuable insights into how organizations successfully mitigate risks and foster resilience. These examples highlight the tangible benefits of a strategic approach to information technology risk management.
A global telecommunications company, facing the immense challenge of replacing its existing network across numerous international locations, adopted a rigorous risk management approach. The project’s complexity and the potential for significant delays necessitated a dynamic risk register and continuous assessment of potential threats. By prioritizing detailed risk modeling and impact assessments, the company ensured that strategic planning and robust control mechanisms were embedded throughout the extensive transformation, helping to navigate unforeseen challenges and achieve operational continuity.
In another instance, a mid-sized regional grocery retailer, mandated by its Board of Directors to enhance its risk management activities, focused on strengthening its IT governance. The IT department, working closely with the board, implemented more comprehensive risk assessment methodologies and established clear protocols for managing data security across its operations. This proactive step not only addressed compliance requirements but also significantly improved the overall resilience of its IT infrastructure against potential cyber threats and operational disruptions.
Similarly, a technology services provider leveraged specialized platforms to manage vulnerability and IT risk management reporting for its global customer base. This allowed them to track vulnerabilities by account, status, and over time, identify commonalities across multiple customers, and effectively coordinate with customers and their vendors for remediation. This proactive and centralized approach to vulnerability management significantly improved their ability to track and mitigate risks, including the critical process of formal risk acceptance. These examples underscore that strong information technology risk and controls are fundamental to safeguarding operations and reputation in complex digital environments.
Conclusion
The digital landscape, while offering unparalleled opportunities, also presents a relentless barrage of threats that demand continuous vigilance. Mastering information technology risk and controls is no longer optional; it is a fundamental pillar of sustainable business growth and operational resilience.