Technology is the backbone of modern business, driving innovation, efficiency, and global connectivity. Yet, this intricate digital web also introduces a constantly evolving landscape of vulnerabilities. As organizations increasingly rely on complex IT infrastructures, the imperative to understand and manage information technology risks and controls has never been more critical. Daily98news will guide you through the intricate world of digital threats, exploring how businesses can not only defend against sophisticated attacks but also proactively build resilient systems. This deep dive aims to demystify buzzwords, providing practical insights for intelligent investment and adoption decisions, ensuring you are equipped to master the digital frontier.
The evolving landscape of digital threats
The digital realm is a battleground where threats evolve at an alarming pace, challenging even the most fortified defenses. The pervasive nature of technology means that while benefits like operational productivity and business growth are abundant, new threats emerge daily. Executives globally rank cyber-attacks among their top worries, with criminals capable of far more than simple email hacks, often bringing entire systems down and holding organizations to ransom. This escalating sophistication highlights a crucial shift: cybersecurity is no longer merely an IT department concern but a fundamental business imperative impacting reputation, finances, and continuity. The average global cost of a data breach has reached $4.88 million in 2024, a 10% increase, reaching $6.08 million. These figures underscore the urgent need for robust information technology risks and controls.
Understanding key information technology risks
Identifying and categorizing the diverse array of threats is the first step in constructing an effective defense. Information technology risks can stem.
Cyber-attacks and data breaches
Malicious software, or malware, remains a prevalent threat, capable of stealing or corrupting business information, causing system failures, or secretly recording computer activity. Ransomware, a particularly insidious form, blocks access to systems or files until a ransom is paid, with a single massive attack in 2017 affecting over 100,000 organizations and costing billions. Data breaches, which involve unauthorized access and theft of sensitive information, often target weak credentials, compromised assets, or third-party access points. In 2024, at least 35.5% of data breaches originated from third-party compromises, a significant increase, 88% of cybersecurity breaches involve an element of human error, highlighting the importance of employee education.
Cloud computing vulnerabilities
The widespread adoption of cloud computing, while offering scalability and flexibility, introduces new complexities and risks. Data breaches are a major concern in cloud environments, frequently caused by misconfigurations, weak access controls, or insufficient encryption. Unsecured APIs and interfaces also present significant entry points for attackers to gain access to cloud services. Other common cloud security risks include insider threats, Distributed Denial of Service (DDoS) attacks, and “shadow IT” where unauthorized cloud applications are used without IT oversight.
Internet of things (IoT) security challenges
The proliferation of IoT devices,. These devices can serve as gateways to an entire network if compromised or be assimilated into botnets for large-scale attacks. Outdated firmware and insufficient update mechanisms further exacerbate these vulnerabilities.
Human error and social engineering
Human error is consistently cited as a significant factor in cybersecurity incidents, contributing to 88% of breaches. Social engineering tactics, such as phishing, pretexting, and baiting, manipulate individuals into divulging sensitive information or taking actions that compromise security. These attacks exploit human trust and curiosity, often leading to the download of malware or disclosure of credentials. Even the most robust technical controls can be bypassed by successful social engineering, making employee education a critical defense.
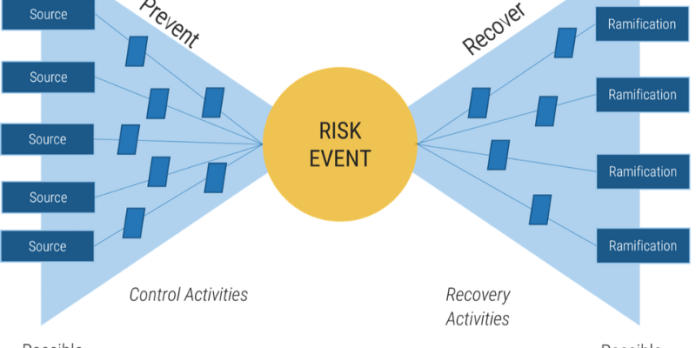
Establishing robust information technology controls

Effective management of information technology risks and controls requires a multi-layered, proactive approach. Controls are specific activities or procedures designed to minimize risk, ensure compliance, and achieve IT objectives. They can be automated or manual, high-level policies or specific actions, and are crucial for maintaining the confidentiality, integrity, and availability of data.
Technical and administrative controls
Technical controls are the technological safeguards implemented to protect IT systems and data. Examples include robust firewalls to prohibit unauthorized network access, antivirus software with daily updates, and intrusion detection systems to monitor and prevent unwanted access. Logical access controls, such as complex passwords, multi-factor authentication (MFA), and least-privilege access, are essential for managing who can access what data based on their role and responsibilities. Furthermore, change management procedures ensure that all modifications to IT systems are authorized and meet business requirements, while source code and document version control protect the integrity of program code.
Administrative controls focus on policies, procedures, and organizational structures. Comprehensive compliance training for all IT staff, along with regular refresher courses, is vital for fostering a security-aware culture. Segregation of duties, which ensures that no single person has control over an entire process, helps prevent fraud and errors. Incident management and problem management policies are critical for addressing operational errors and identifying root causes to prevent recurrence.
Governance and compliance frameworks
Adopting recognized governance and compliance frameworks provides a structured approach to managing IT risks. The NIST Cybersecurity Framework (CSF) is a voluntary framework developed by the National Institute of Standards and Technology, offering guidelines to identify, protect, detect, respond to, and recover, and continually improving an Information Security Management System (ISMS). It is more prescriptive than NIST CSF, requiring specific documentation and processes, and offers global recognition through certification. While distinct, these frameworks are complementary; implementing both can provide a comprehensive strategy, with ISO 27001 offering structure and NIST CSF enhancing risk management flexibility. Both emphasize top management support, continuous improvement, and a risk-based approach.
Leveraging emerging technologies for risk mitigation
The same technological advancements that introduce new risks also offer powerful tools for enhancing information technology risks and controls. Emerging technologies like Artificial Intelligence (AI), Machine Learning (ML), and Blockchain are revolutionizing how organizations approach cybersecurity, enabling more proactive and sophisticated defense mechanisms.
Artificial intelligence and machine learning
AI and ML are transforming cybersecurity by enhancing threat detection, response, and prevention capabilities. These intelligent algorithms can analyze vast amounts of data at speeds and scales beyond human capacity, identifying patterns and making informed decisions. AI-powered systems can detect threats in real-time, automate routine tasks like log analysis and vulnerability scanning, and continuously learn.
Key applications include:
- Automated threat detection and analysis: AI and ML quickly identify suspicious trends, malware, or indicators of malicious intrusion by analyzing real-time data on a massive scale.
- Predictive threat intelligence: Machine learning models analyze historical attack data and current threat feeds to anticipate future attacks, enabling organizations to proactively strengthen defenses.
- Improved vulnerability management: AI helps organizations assess systems more effectively, identify high-risk areas, and improve problem-solving to address vulnerabilities before they escalate.
While AI offers immense benefits, its adoption in cybersecurity also introduces new complexities and potential vulnerabilities, such as AI-powered attacks and ethical concerns, necessitating secure and responsible AI policies.
Blockchain’s role in security
Blockchain technology offers a different paradigm for security, characterized by decentralization, transparency, and immutability, which inherently resist data tampering and reduce the risk of cyberattacks. Its distributed ledger makes it incredibly difficult for hackers to alter records without the consensus of the entire network, providing stronger data protection than centralized systems.
Blockchain’s advantages for cybersecurity include:
- Enhanced data integrity: Once data is recorded on a blockchain, it cannot be changed without the network’s consensus, ensuring data reliability and transparency.
- Decentralized identity management: By decentralizing identity data storage, blockchain reduces the risk of identity theft and fraud, giving users more control over their personal information.
- Eliminating single points of failure: The distributed nature of blockchain removes centralized vulnerabilities that hackers typically exploit, making it significantly harder to compromise the entire dataset.
- Securing IoT ecosystems: Blockchain can provide a secure and scalable framework for communication between IoT devices, protecting against unauthorized access and data breaches.
While robust, vulnerabilities can still exist in smart contracts, third-party applications, or private keys, emphasizing the need for pro.
Case studies in effective risk management

Real-world examples demonstrate the tangible impact of robust information technology risks and controls. Organizations that prioritize and strategically implement risk management frameworks often see significant improvements in their security posture and resilience.
A notable instance involved a financial institution that integrated an advanced risk identification framework, leading to a 45% decrease in data breaches within a year. Leveraging advanced analytics and machine learning, this entity not only accelerated threat identification but also improved incident response times by 30%. This showcases how a combination of strategic framework adoption and technological investment can yield substantial protective benefits and cost savings in breach recovery.
Another compelling case highlights a major retailer that successfully reduced cybersecurity incidents by over 50% by adopting a layered defense strategy. This included rigorous third-party audits and comprehensive employee training, addressing the often-overlooked human element and supply chain vulnerabilities. The increasing reliance on third-party vendors means that at least 98% of organizations have at least one vendor that has experienced a data breach, making third-party risk management an undeniable priority. These examples illustrate that continuous risk assessment, combined with investment in both technology and human capital, is paramount for building resilience in the face of evolving digital threats.
Final thoughts
The dynamic landscape of information technology risks and controls demands continuous vigilance and strategic adaptation. Daily98news encourages you to not merely react to emerging threats but to embrace a forward-thinking approach, integrating cutting-edge technologies like AI and Blockchain while reinforcing foundational controls and fostering a culture of security awareness. By understanding the intricate interplay of threats and safeguards, and by making informed decisions about technology adoption and investment, you can transform potential vulnerabilities into opportunities for enhanced resilience and competitive advantage. Keep exploring, keep learning, and stay ahead in the ever-evolving digital age.